Brendan Dolan-Gavitt
-
Associate Professor

Brendan Dolan-Gavitt is an Associate Professor in the Computer Science and Engineering Department at NYU Tandon. He holds a Ph.D. in computer science from Georgia Tech (2014) and a BA in Math and Computer Science from Wesleyan University (2006).
Dolan-Gavitt's research interests span many areas of cybersecurity, including program analysis, virtualization security, memory forensics, and embedded and cyber-physical systems. His research focuses on developing techniques to ease or automate the understanding of large, real-world software systems in order to develop novel defenses against attacks, typically by subjecting them to static and dynamic analyses that reveal hidden and undocumented assumptions about their design and behavior.
His work has been presented at top security conferences such as USENIX Security, the ACM Conference on Computer and Communications Security (CCS) and the IEEE Symposium on Security and Privacy. He also led the development of PANDA, an open-source platform for architecture-neutral dynamic analysis, which has users around the world and has been featured in technical press such as The Register. Prior to joining NYU, he was a postdoctoral researcher at Columbia University.
Education
Georgia Institute of Technology 2014
Doctor of Philosophy, Computer Science
Wesleyan University 2006
Bachelor of Arts, Computer Science and Mathematics
Publications
Journal Articles
Brendan Dolan-Gavitt, Patrick Hulin, Engin Kirda, Tim Leek, Andrea Mambretti, Wil Robertson, Frederick Ulrich, Ryan Whelan. LAVA: Large-scale Automated Vulnerability Addition. Proceedings of the IEEE Symposium on Security and Privacy (Oakland), May 2016.
Brendan Dolan-Gavitt, Josh Hodosh, Patrick Hulin, Tim Leek, and Ryan Whelan. Repeatable Reverse Engineering with PANDA. Program Protection and Reverse Engineering Workshop (PPREW), December 2015.
Brendan Dolan-Gavitt, Tim Leek, Josh Hodosh, and Wenke Lee. Tappan Zee (North) Bridge: Mining Memory Accesses for Introspection. Proceedings of the ACM Conference on Computer and Communications Security (CCS), November 2013.
Brendan Dolan-Gavitt, Tim Leek, Michael Zhivich, Jonathon Giffin, and Wenke Lee. Virtuoso: Narrowing the Semantic Gap in Virtual Machine Introspection. Proceedings of the IEEE Symposium on Security and Privacy (Oakland), May 2011.
Brendan Dolan-Gavitt, Abhinav Srivasta, Patrick Traynor, and Jonathon Giffin. Robust Signatures for Kernel Data Structures. Proceedings of the ACM Conference on Computer and Communications Security (CCS), November 2009.
Brendan Dolan-Gavitt. The VAD tree: A process-eye view of physical memory. Digital Investigation, Volume 4, Supplement 1, September 2007, Pages 62-64.
Brendan Dolan-Gavitt. Forensic analysis of the Windows registry in memory. Digital Investigation, Volume 5, Supplement 1, September 2008, Pages S26-S32.
Other Publications
Brendan Dolan-Gavitt, Bryan Payne, and Wenke Lee. Leveraging Forensic Tools for Virtual Machine Introspection. Technical Report: GT-CS-11-05, May, 2011.
Brendan Dolan-Gavitt and Yacin Nadji. See No Evil: Evasions in Honeymonkey Systems. May 2010.
Brendan Dolan-Gavitt and Patrick Traynor. Using Kernel Type Graphs to Detect Dummy Structures. December 2008.
Research News
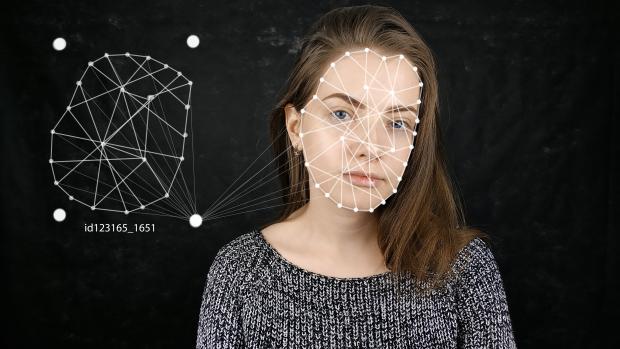
Studying the online deepfake community
In the evolving landscape of digital manipulation and misinformation, deepfake technology has emerged as a dual-use technology. While the technology has diverse applications in art, science, and industry, its potential for malicious use in areas such as disinformation, identity fraud, and harassment has raised concerns about its dangerous implications. Consequently, a number of deepfake creation communities, including the pioneering r/deepfakes on Reddit, have faced deplatforming measures to mitigate risks.
A noteworthy development unfolded in February 2018, just over a week after the removal of r/deepfakes, as MrDeepFakes (MDF) made its entrance into the online realm. Functioning as a privately owned platform, MDF positioned itself as a community hub, boasting to be the largest online space dedicated to deepfake creation and discussion. Notably, this purported communal role sharply contrasts with the platform's primary function — serving as a host for nonconsensual deepfake pornography.
Researchers at NYU Tandon led by Rachel Greenstadt, Professor of Computer Science and Engineering and a member of the NYU Center for Cybersecurity, undertook an exploration of these two key deepfake communities utilizing a mixed methods approach, combining quantitative and qualitative analysis. The study aimed to uncover patterns of utilization by community members, the prevailing opinions of deepfake creators regarding the technology and its societal perception, and attitudes toward deepfakes as potential vectors of disinformation.
Their analysis, presented in a paper written by lead author and Ph.D. candidate Brian Timmerman, revealed a nuanced understanding of the community dynamics on these boards. Within both MDF and r/deepfakes, the predominant discussions lean towards technical intricacies, with many members expressing a commitment to lawful and ethical practices. However, the primary content produced or requested within these forums were nonconsensual and pornographic deepfakes. Adding to the complexity are facesets that raise concerns, hinting at potential mis- and disinformation implications with politicians, business leaders, religious figures, and news anchors comprising 22.3% of all faceset listings.
In addition to Greenstadt and Timmerman, the research team includes Pulak Mehta, Progga Deb, Kevin Gallagher, Brendan Dolan-Gavitt, and Siddharth Garg.
Timmerman, B., Mehta, P., Deb, P., Gallagher, K., Dolan-Gavitt, B., Garg, S., Greenstadt, R. (2023). Studying the online Deepfake Community. Journal of Online Trust and Safety, 2(1). https://doi.org/10.54501/jots.v2i1.126