A strong, ongoing partnership between industry and academia
Google’s latest show of support came at NYU Tandon’s CSAW

Mariana Raykova, a research scientist from Google’s Private Computing Group gave the keynote at CSAW 2023
This month, Google lent some star power to CSAW 2023, Tandon’s annual cybersecurity competition, held since 2003 and now the most comprehensive student cyber event of its type.
This year’s CSAW was keynoted by Mariana Raykova, a research scientist from Google’s Private Computing Group, who explained her work with privacy-enhancing technology for protected computing to a packed crowd of CSAW participants from around the world.
Raykova, who sat on the Privacy Preserving Techniques Task Team that advised the U.N. Global Working Group on Big Data in the preparation of its handbook on the topic, stressed Google’s commitment to anonymizing the personal data in its datasets – even as those datasets get increasingly larger.
Her presence only strengthened the longstanding connection between the iconic company and the school: This summer, for example, Google announced the company’s Cyber NYC Institutional Research Program, aimed at stimulating the cybersecurity ecosystem and establishing New York City as the global leader in cybersecurity. As part of the initiative, NYU Tandon is receiving $1 million in annual funding, each year through 2025 in order to grow its cybersecurity degree programs, bolster the future workforce, and champion underrepresented groups in cybersecurity.
Earlier this year, top-level figures from Google, including Senior Engineering Director Todd Underwood and CIO Phil Venables (also a Tandon Board Member), came to Brooklyn to take part in a panel–attended by hundreds of students–to discuss the future of the field.
Other supporters, other voices
Raykova was a major draw in an impressive CSAW line-up of expert speakers that also included:
- Dan Guido, the CEO and founder of Trail of Bits, who discussed how AI is impacting cybersecurity. (Guido earned his bachelor’s degree from NYU Tandon in 2008 and has also served as an adjunct professor and hacker-in-residence; he was involved in CSAW from its earliest inception, making his appearance in 2023 something of a two-decade, full-circle moment; he has said: “CSAW played a large part in how I came to love cybersecurity, and I'm glad it still does to so many students.”)
- Patrick Schlapfer, a Senior Malware Analyst at HP Labs, who gave an evocative presentation on what he called “the Wild West” of cybercrime
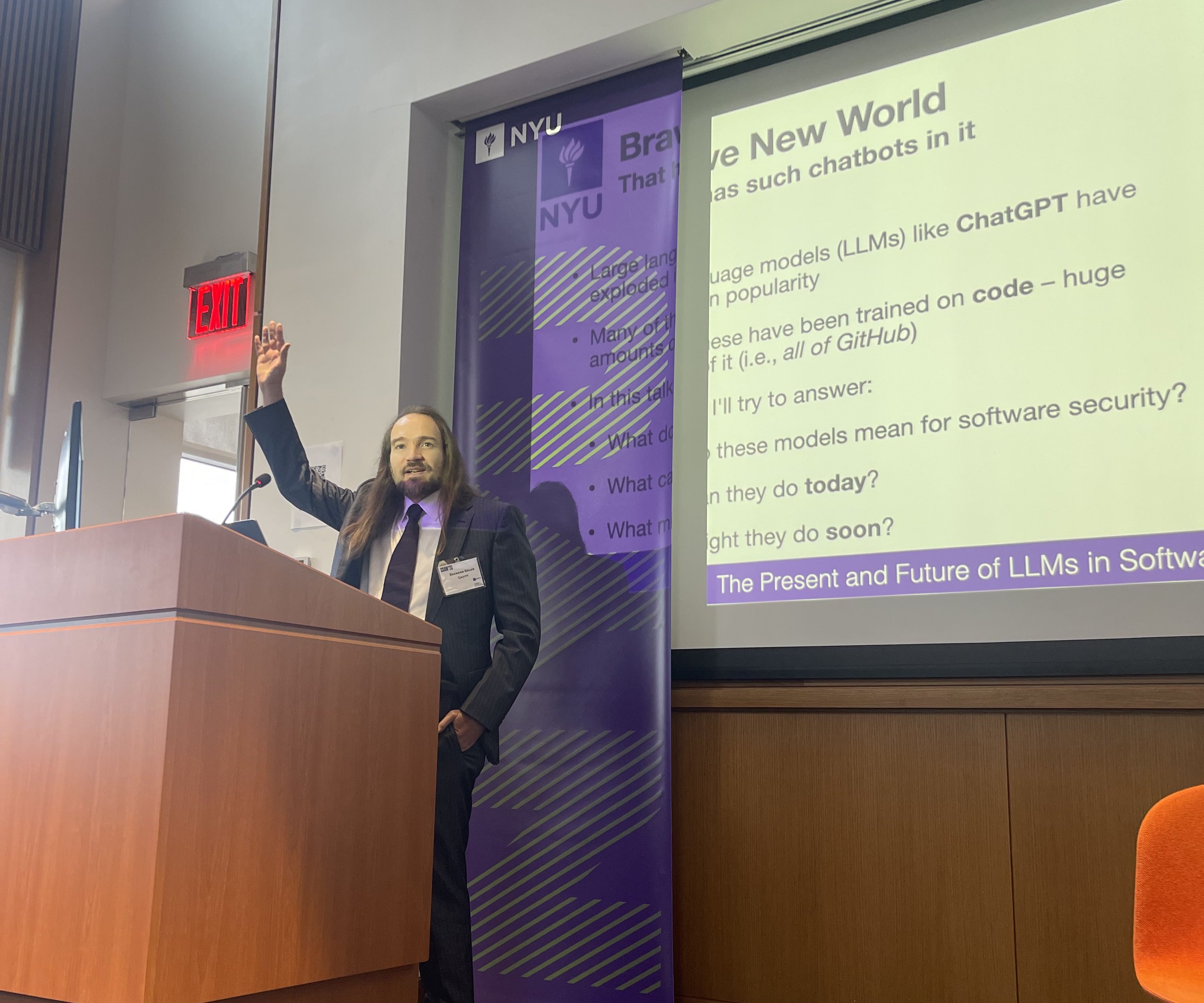
- NYU Tandon Associate Professor of Computer Science and Engineering Brendan Dolan Gavitt, whose researches focuses on developing techniques to ease or automate the understanding of large, real-world software systems in order to develop novel defenses against cyberattacks
Google was far from the only industry leader lending their backing to CSAW: in addition to HP and Trail of Bits, other sponsors included snyk; the MTA; Darktrace; TIAA; efabless; ConEd; NYSTAR; the NSF; Synopsys; T. Rowe Price; Zellic; and The Depository Trust & Clearing Corporation (DTCC), which recently partnered with Tandon in expanding the school’s Center for Cybersecurity to include a major area of expertise in resiliency – with most sending representatives to review resumes and discuss internship and employment opportunities with some 200 students who attended the CSAW Career Fair.
The games at a glance
As impressive as the industry presentations and career fair, few would argue that the most riveting part of CSAW remains the variety of heated competitions, which collectively drew almost 600 finalists from around the globe.
They included:
The AI Hardware Attack Challenge, which called upon participants to use generative AI to insert a hardware vulnerability, such as a trojan or backdoor, into an open-source digital design of their choice – with points awarded for subtle yet powerful exploits, such as those that allow system compromise from userspace.
The Applied Research Competition, for published papers with practical application.
BioHack 3D, which involved brainstorming ingenious attacks on biochips, cunningly designed to slip past post-manufacturing security checks unnoticed.
One of the oldest and largest Capture the Flag events in the world, routinely drawing well over 1,000 teams in its initial rounds.
The Embedded Security Challenge, first run in 2008 and the oldest hardware security competition in the world, with this year’s edition focusing on side channel attacks on critical cyber-physical systems.
Hack 3D, aimed at students interested in the security of additive manufacturing systems.
Hack My Robot, organized by the S.M.A.R.T. Construction Research Group with support and collaboration from the Center for Cybersecurity (CCS) at NYUAD and the Center for AI and Robotics (CAIR) at NYUAD.
The LLM Attack Challenge, which recognized the burgeoning popularity of large language models (LLM) and their ability to pinpoint the vulnerabilities in software and generate code to attack it.
Logic Locking, which tested students’ facility with a revolutionary technique for protecting the intellectual property of integrated circuits from myriad security threats.
Fun Facts
- Registrants: 931
- Research posters on display: 40
- Global embedded security teams: 20
- Teams attempting logic locking: 7
- Most solves by the top embedded security teams: 6 out of 6
- Teams in Capture the Flag finals: 51
- Length of Capture the Flag finals: 36 hours
- Top-three Capture the Flag Teams: Team sigpwny (University of Illinois Urbana-Champaign), Team GreyHat (Georgia Institute of Technology), Team StackPhish (Arizona State University, Northeastern University, UC Santa Barbara)