Researchers design genetic barcodes that authenticate DNA fingerprints
NYU Tandon researcher Ramesh Karri collaborated with Duke University experts to propose a way of ensuring that genetic samples taken in the field for DNA fingerprinting arrive at the laboratory unaltered
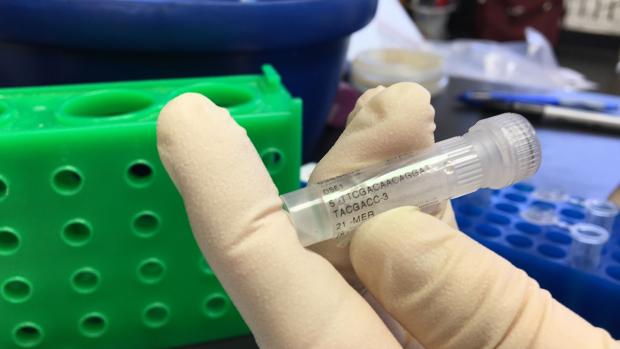
DNA fingerprinting sample
BROOKLYN, New York, Tuesday, May 27, 2019 – DNA fingerprinting, a key process in a nearly $10 billion global business that includes players like 23andMe and AncestryDNA, identifies individuals from very small spans of their genetic material. This roughly 0.1% of the human genome unique to each individual can also be used to prove that a DNA sample has not been tampered with or swapped between collection and delivery to labs, a risk researchers identified a decade ago.
In a new study, “Molecular Barcoding as a Defense against Benchtop Biochemical Attacks on DNA Fingerprinting and Information Forensics,” which appeared online on May 14 in the journal IEEE Transactions on Information Forensics and Security, a team of researchers at NYU Tandon, Duke University and Intel demonstrated a system for doing this by creating “genetic barcodes” based upon these tiny regions.
Besides Ramesh Karri, NYU Tandon Professor of electrical and computer engineering, the team comprised Duke researchers Krishnendu Chakrabarty, the John Cocke Distinguished Professor of Electrical and Computer Engineering; Kristin Scott, an assistant research professor; Mohamed Ibrahim, now at Intel Corporation; and Tung-Che Liang, a Ph.D. student at Duke.
The team relied on a technique called polymerase chain reaction (PCR). In DNA fingerprinting, PCR replicates the genetic sequences at these unique-DNA sites repeatedly so that they can easily be read. Based on the specific combinations of nucleic acids at these various sites, genetic samples can be matched to their sources.
The process by which the team built genetic barcodes included adding two short stretches of synthetic DNA to samples. Because they are synthesized, they can comprise most any combination of the four available base pairs imaginable. And at 280 and 190 base pairs each, the chances of correctly guessing the genetic combination is vanishingly small.
Karri and his collaborators at Duke and Intel came up with a realistic threat model wherein an adversary intercepts and forges a sample during transfer from the field to the forensics lab. They then analyzed the conditions an adversary needs to satisfy in order to undermine the barcoding system.
Said Karri, who is a co-founder and co-chair of the NYU Center for Cyber Security, “These conditions are related to the physical characteristics of the molecular barcode. By linking these conditions back to how barcodes are generated and the expansiveness of the search space, we show that the probability that an adversary can discover the barcode is negligibly low.”
“If you think about conventional encryption techniques, like security for a smartphone, there’s usually a passcode that only one person knows,” said Ibrahim. “Our idea is to inject non-harmful material into genetic samples immediately when they are collected in the field that act as a similar password. This would ensure that the samples are authentic when they reach the processing stage.”
To interpret the barcodes, technicians at the trusted destination laboratory would employ a PCR machine to repeatedly copy a specific segment of DNA, a process that can be done only if the machine can identify where the DNA sequence starts and ends. Primers, which the investigators must send securely to the technicians in the laboratory, provide that information, and without it, an attacker would have no chance of amplifying the correct barcodes.
Once the technicians finish an initial PCR run with the samples and primers provided, the two barcodes appear as peaks or lines in the resulting genetic data, depending on the method being used to identify them. To make sure the samples are authentic and not tampered with, the technicians must simply make sure these two barcodes appear as expected.
“When the right primers are used to unlock a barcode, you should get a positive result,” said Ibrahim. “If you don’t, then that means that the sample is not genuine. Some sort of switching or alteration has occurred.”
While this system currently relies on information being transmitted securely to the laboratory, the researchers say there are ways that the genetic barcodes could be streamlined into the technology. For example, the barcodes could be correlated in some way to the samples being sent, and technicians could look up the correct primers to use from a database. With the proper hardware, the idea could also conceivably be translated into the chips running the DNA analysis themselves.
This research was supported by the Army Research Office (W911NF-17-1-0320) and the National Science Foundation (CNS-183362).
Note: Images available at https://nyutandon.photoshelter.com
About the New York University Tandon School of Engineering
The NYU Tandon School of Engineering dates to 1854, the founding date for both the New York University School of Civil Engineering and Architecture and the Brooklyn Collegiate and Polytechnic Institute (widely known as Brooklyn Poly). A January 2014 merger created a comprehensive school of education and research in engineering and applied sciences, rooted in a tradition of invention and entrepreneurship and dedicated to furthering technology in service to society. In addition to its main location in Brooklyn, NYU Tandon collaborates with other schools within NYU, one of the country’s foremost private research universities, and is closely connected to engineering programs at NYU Abu Dhabi and NYU Shanghai. It operates Future Labs focused on start-up businesses in downtown Manhattan and Brooklyn and an award-winning online graduate program. For more information, visit engineering.nyu.edu.