New version of Uptane Standard clarifies protection strategies for vulnerable vehicles
With the release of a clearer and more consistent standard, Uptane, an NYU Tandon School of Engineering software project, is better poised to defend vehicle computers against malicious actions.
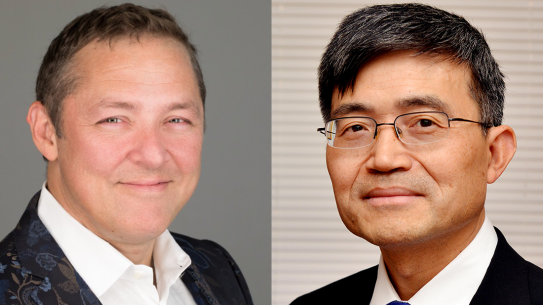
Uptane was co-developed by Justin Cappos, professor of computer science and engineering.
BROOKLYN, New York, Wednesday, January 13, 2021 – The recent SolarWinds hack, in which companies, government agencies, and academic institutions suffered significant data breaches after malware was slipped into a software update, is a sobering reminder that, though updates are necessary, they are also always fraught with risk.
Onboard computing units in cars are similarly vulnerable. The 2020 Global Automotive Cybersecurity Report, released by UpStream Security in December 2020, notes a 99% increase in cyberattacks on vehicles from 2018 to 2019, and these attacks have increased 700% since 2016.
Uptane, founded at NYU Tandon in 2016 by Justin Cappos, associate professor of computer science and engineering at the NYU Tandon School of Engineering, and Trishank Kuppusamy, who was a Ph.D. student at the time, is an open-source software security project designed to address this threat. With direct input from automotive manufacturers and suppliers, its implementations secure automotive systems by establishing a set of checks and balances on a vehicle’s electronic control units (ECUs) to ensure the authenticity of incoming software updates. Among its adoptions, Uptane is part of Automotive Grade Linux, an open-source system currently used by many large automakers, and has been implemented by suppliers including Airbiquity and HERE.
This month the Uptane framework releases its first update to the standard, representing roughly 18 months of careful review by the Uptane Standards team, comprising a cross-section of auto manufacturers, tier 1 suppliers, and representatives of academia and government regulatory agencies. In particular, the new version was reviewed with an eye towards compliance with proliferating regulations and international standards within the automotive industry.
“The emergence of these comprehensive automotive cybersecurity standards and regulations offers a historic opportunity to dramatically improve the cybersecurity and safety of new vehicles,” says security consultant Ira McDonald, who has been an invited expert in the Trusted Computing Group since 2006 and is an Uptane Steering Committee member.
“Nation-state actors have increasingly attacked software delivery mechanisms and the software supply chain,” said Cappos. “Without strong protections like Uptane, these attacks against the automotive industry will be successful, leading to massive damage and loss of life.”
The new version of the Uptane Standard, which can be reviewed at uptane.github.io/papers/uptane-standard.1.1.0, will be accompanied for the first time by a version-controlled Deployment Best Practices companion document. While most of the information in this latter document has been available on the Uptane website for several years, this deployment guidance is now being released as a stand-alone document at the request of auto manufacturers. Future releases of the Uptane Standard will be paired with an updated version of the Uptane Deployment Best Practices document.
Patti Vacek, a software engineer behind one of the first open-source Uptane implementation from Here Technologies, explained, “These best practices have been informed by years of experience of putting the Standard into action. Our partners have found this information to be a useful extension to the Standard, especially when it comes to making important decisions about trade-offs and real-world implementation details.”
Uptane was initially developed under a grant from the U.S. Department of Homeland Security by a team of engineers at NYU Tandon, the University of Michigan Transportation Research Institute in Ann Arbor, and the Southwest Research Institute in Austin, TX. Over a four-year period, more than 30 individuals and 17 organizations have provided input to the design, development, and implementation of Uptane. A full list of contributors to the project can be found here (uptane.github.io/people)
Cappos and his lab are affiliated with the NYU Center for Cybersecurity research center at NYU Tandon. Uptane is a Joint Development Foundation project of the Linux Foundation, operating under the formal title of Joint Development Foundation Projects, LLC, Uptane Series.
About the NYU Center for Cybersecurity
The NYU Center for Cybersecurity (CCS) is an interdisciplinary research institute dedicated to training the current and future generations of cybersecurity professionals and to shaping the public discourse and policy, legal, and technological landscape on issues of cybersecurity. NYU CCS is a collaboration between NYU School of Law, NYU Tandon School of Engineering, and other NYU schools and departments. For more information, visit cyber.nyu.edu.
About the New York University Tandon School of Engineering
The NYU Tandon School of Engineering dates to 1854, the founding date for both the New York University School of Civil Engineering and Architecture and the Brooklyn Collegiate and Polytechnic Institute. A January 2014 merger created a comprehensive school of education and research in engineering and applied sciences as part of a global university, with close connections to engineering programs at NYU Abu Dhabi and NYU Shanghai. NYU Tandon is rooted in a vibrant tradition of entrepreneurship, intellectual curiosity, and innovative solutions to humanity’s most pressing global challenges. Research at Tandon focuses on vital intersections between communications/IT, cybersecurity, and data science/AI/robotics systems and tools and critical areas of society that they influence, including emerging media, health, sustainability, and urban living. We believe diversity is integral to excellence, and are creating a vibrant, inclusive, and equitable environment for all of our students, faculty and staff. For more information, visit engineering.nyu.edu.