First Ever Conference on Biochip Security Sees Risks and Rewards at the Nexus of Biochemical and Electrical Engineering

ARO Workshop on Secure and Trustworthy Biochips Attendees
Today there are some 10 billion connected devices — excluding smartphones and computers — and those numbers are growing fast. One driver: mobile applications for medical devices, including biochips (devices that combine biochemistry and electrical and computer processing to run chemical reactions — sometimes many at once at the microscopic level). Paired with microfluidic systems, these “lab on a chip” technologies could revolutionize remote sensors, environmental sampling procedures, and medical tests for coagulation, blood gas electrolytes, hematology, urine chemistry, cardiac markers, and more.
However, as the ill-fated trajectory of the bioscience startup Theranos demonstrates, such diagnostic devices at the nexus of electrical engineering and biochemistry are complex and rife with opportunities to fake results, or hack, steal, corrupt and counterfeit components. More so because many of these systems are connected to other devices via the web.
“The attack surface is massive,” said Ramesh Karri, professor of electrical and computer engineering at NYU Tandon School of Engineering. Karri was one of the organizers of the ARO Workshop on Secure and Trustworthy Biochips at NYU Tandon on August 24, 2018, the first-ever conference to examine the threats and security vulnerabilities unique to biochips.
Besides Karri, who is co-chair and co-founder of the NYU Center for Cybersecurity, which hosted the event, organizers included Krishnendu Chakrabarty, Chair of the Department of Electrical and Computer Engineering at Duke University; and Cliff Wang, Director of the Computer Science Division of the U.S. Army Research Office (ARO).
“Attackers can come from anywhere,” said Karri. “The chemistry, the sample, the biology, the protocol, the surface, the network hardware and software. And if the chip is implanted in a patient or part of a wearable system, the stakes are life and death.”
While presenters at the conference delved into innovative systems employing biochips and microfluidics, they also explored the threat landscape for such processes as digital microfluidics, which uses electronics to do Pacman-like manipulations of microscopic drops of fluid in tiny capillaries etched onto silicon chips. Healthcare is driving microfluidics deployment, a segment analysts say could hit $4 Billion by 2020.
As Yuksel Temiz, a researcher at IBM Research Zurich predicted during his presentation, “I think in the near future we will see gadgets for infectious diseases, biohazards, drug discovery, agriculture and more. It’s a very diverse application area.”
But Temiz also discussed the ease with which a counterfeiter today can simply repackage pregnancy tests by using the original container and substituting in a new test fabric. “We have heard stories about people cleaning and repackaging a previously used test. You can find these on Alibaba or eBay, and it’s almost impossible to know if it’s genuine or counterfeit.”
IBM, he noted, is working on security codes implemented inside the assay, not just on the package. These dynamic codes are altered by the sample itself because the codes are written in water-soluble ink.
“So, as the sample moves you get a new code,” said Temiz. “Because these are water-soluble ink dots in a pattern, there is so no way to go back to initial code.”
William Grover of the University of California, Riverside focused on the need for security at the interface between electronic parts and flow-driven chemical systems, a unique intersection typical of devices employing biochips. He described something of a ‘steampunk’ approach to securing electric/non-electric interface, based on an on-chip set of microscopic pumps constituting non-electric computers, using valve-based pneumatic logic designed to detect errors rather than electronic connections.
A key presentation involved a new research collaboration between NYU Tandon, ARO and Duke University on investigating a means of securing benchtop chemistry for whole blood bioassays, in which strands of DNA play — literally — a key role.
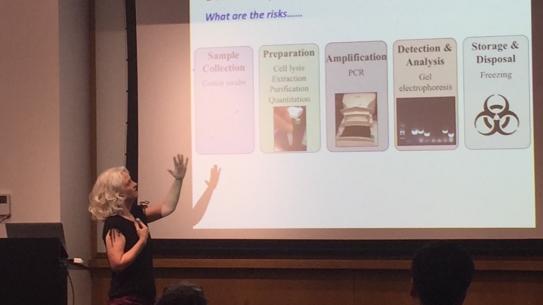
Kristin Scott, a research professor at Duke University School of Medicine explained how the innovative use of DNA strands can identify stealthy DNA forgery attacks: the double-stranded piece of DNA serves as a macro-molecular barcode, and another strand of genetic material matching the DNA serves as the key, or “primer.”
Imagine an athlete giving a blood sample for drug testing,” she explained. “Right then and there the clinician injects the DNA into the sample, which gets sealed in solution along with the sample itself,” she said. “The barcode does not alter the sample, it just goes along for the ride. When it gets to the lab whoever is doing the research has a list of unique primers, or keys, for each sample.” A chemical system either halts the test or allows it to continue based on these results.
Scott explained that the method — which employs a multi-cycle process called a polymerase chain reaction (PCR) to exponentially increase the amount of genetic material — might be seen as “upstream” of the intricate microfluidic assays that also need to be secured, meaning sample validation constitutes a first line of defense. “You could use this in a range of scenarios, including a crime scene or clinical trials. It’s another layer of security.”
Chakrabarty said the conference itself sprang from Karri’s efforts to secure funding from the ARO for this DNA-based benchtop forensics.
“Part of the plan of our research was to hold a workshop and create community,” he said. “It started with two people with one small grant and the idea is that we would invite like-minded researchers from different communities like computing microfluidics and biology.
Karri added that companies like IBM and Baebies, Inc., which builds compact digital microfluidic platforms for near-patient screening and diagnostics, are deeply interested because they are concerned about the security of their own intellectual property and, of course, the validity of patient tests.
Said Scott Norton, Senior Director of Advanced Technology at Baebies Inc., during a description of the architecture of the company’s digital microfluidics capabilities, “The bottom line for us is assuring we have built-in mechanisms that can provide safeguards against any kind of malicious manipulation.”
Other presenters included Jack Tang, an NYU Tandon doctoral student in electrical and computer engineering under Karri, who is working on technologies for securing biochips; Emre Araci of Santa Clara University who spoke about microfluidics for mechanical sensing and in bio-medicine; Rafael Song of NYU Abu Dhabi who explored security for organ-on-a-chip technology; and Douglas Densmore of Boston University, whose presentation explored securing microfluidics for synthetic biology.
The conference demonstrates that NYU Tandon and its collaborators are ahead of the cyber curve on biochips just as the university’s researchers — led by Karri — were over a decade ago when introducing security strategies for integrated circuits, noted Chakrabarty. “Microfluidics is still quite new, and the whole notion of lab-on-a-chip and electronic hardware and software design is even newer, but it is critical to begin thinking about ways of securing these systems.”
The conference concluded with a panel moderated by Jeyavijayan Rajendran of Texas A&M University, who received his Ph.D. in electrical engineering from NYU Tandon. Panelists — including Wang, Norton, Ozgur Sinanoglu of NYU Abu Dhabi, and Sandip Kundu of the University of Massachusetts at Amherst who is a program director at the National Science Foundation — discussed challenges and research opportunities in biochip security.
Karri said the collaborators would like to see the workshops continue as a series at Tandon or at Duke or at partner institutions.
“We have methods in place to secure software and wireless. The challenge is how to secure biology, fluidics and chemistry and how can electronics interface in a secure way — that is the bigger problem right now.”